What Does Texas Shooting Case Tell Us About Subpoenas / Warrants for iPhone & iCloud Information?
- By : Cbh
- Category : 4th Amendment, iOS, Privacy
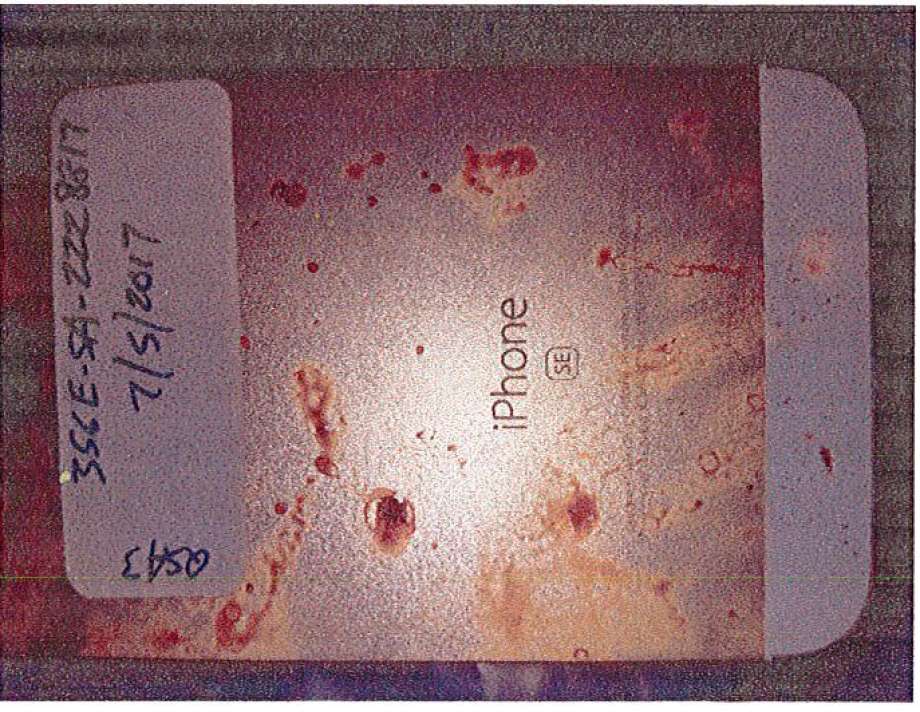
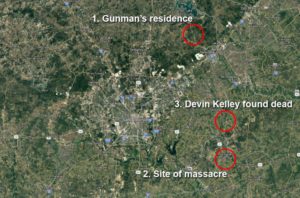
On November 5, 2017, 26-year old Devin Patrick Kelley allegedly shot and killed 26 people at the First Baptist Church in Sutherland Springs, Texas. Mr. Kelley’s body was reportedly recovered from a Ford Expedition; he was found deceased from a single bullet wound (entering above right ear and exiting rear left of skull) and a bloodied iPhone SE was located on the vehicle’s floorboards. A photo of the shooter’s iphone (above) was attached to the probable cause affidavit. Investigating a state charge of capital murder, the Texas Rangers sought and obtained a November 9, 2017 warrant seeking the alleged shooter’s iPhone and iCloud data from Apple. Their response presumably is due on or about Monday, December 11, 2017.
The probable cause affidavit and the search warrant tell us several things about the sophistication of law enforcement in making these requests but it also provides some insight as to what data on your iPhone or in the iCloud is encrypted and possibly unavailable to law enforcement barring exceptional means.
[The following discussion applies to iDevices operating on iOS 8.0 and later. That version of the operating system was released more than three years ago so and iPhones starting with iPhone 6 came with that version pre-installed. More succinctly, if your phone is less than three years old and/or you’re running 8.0 or above, the following applies to you. Earlier phones/iOS versions are less secure. The shooter’s phone, an iPhone SE, is a fairly sophisticated 2016 device which was roughly contemporaneous with the iPhone 6 (smaller screen but it had Touch ID).]
WHAT DID THE WARRANT SEEK FROM APPLE?
The Search Warrant specifically seeks “iCloud accounts identified by the below listed identities, information, and/or devices” and then provided Kelley’s name, DOB, address, phone number, and IMEI/ESN numbers. From January 1, 2016 – November 9, 2017 (notably, the date of the subpoena which was four days after the event), law enforcement sought a list of 14 items you can read here. The highlights include:
- All account information, including IP logs and associated devices
- Photo Stream content and metadata
- iCloud content
- Bookmarks, reading lists, tabs, backups of all Apple devices stored on the iCloud
- Email, Contacts, Calendar, Notes, Reminders
- All activity, connection, and transaction logs (with IP addresses) for any use of FaceTime, iCloud, iTunes, IM, and other services, including Game Center
- “All files, keys or other information necessary to decrypt any data produced in encrypted form, when available to Apple (including, but not limited to keybag.txt and fileinfolist.txt files)”
[the keybag.txt apparently holds the device password and the encryption key while fileinfolist.txt appears to be a device file directory]
A few minor notes: law enforcement was given everything they requested by the court; there was little discussion about the phone itself in the PC affidavit except to claim that they believed Kelley’s information was synced to iCloud (unclear why they believe so) and that the data “could help identify additional witnesses with pertinent information as well as possible motives…”
HOW MIGHT APPLE RESPOND?
According to Apple’s Legal Process Guidelines (June 2017), they list approximately twenty data points which could be produced in response to a proper law enforcement warrant or subpoena. Here are some of the more interesting data assets that Apple may (or may not) produce:
- Device registration – Apple admits that it does not verify this customer information
- iTunes purchases / interactions
- iCloud – “all iCloud data stored by Apple is encrypted at the location of the server. [Apple gives third party vendors the keys except for backup information] Apple retains the encryption keys in its U.S. data centers.”
- Find My iPhone – device location services information is stored on the phone and is unavailable to Apple. However, Find My iPhone connection logs are available to Apple for a period of 30 days.
- Passcode Locked iOS Devices – “Apple does not possess the encryption key.”
- FaceTime / iMessage – “Apple has no way to decrypt Facetime [or iMessage] data. Apple cannot intercept Facetime [or iMessage] communications.” Apple does maintain call and message logs for 30 days.
BOTTOM LINE FOR USER PRIVACY
Users who wish maximum protection for iDevice content should avoid or significantly limit what data is backed up to the iCloud since Apple has the encryption keys and may be compelled to produce that information in response to a valid subpoena or warrant. Content on an iDevice should be password protected (and thereby encrypted) with the password safely stored or memorized.
Current versions of iOS allow for quick disabling of FaceID and TouchID so that users can enjoy the convenience but swiftly disable that feature (see here). Be mindful that recent court decisions suggest that courts can compel production of passwords (or hold the person in contempt) and, for more serious crimes like the Texas or San Bernadino shootings, it appears that FBI and intelligence agencies may have the resources to overcome phone encryption. However, setting aside extreme examples, maintaining good password protection AND leaving content on the phone appears to be the current best method to maintain privacy.
Image credit: San Antonio Express-News